Connecting state and local government leaders
A Greek team found they could interrupt and even falsify data.
Networked sensor systems that measure seismic activity are vulnerable to hacking, which could have implications from monitoring nuclear tests to planning for disaster relief, according to Greek researchers.
The data integrity of seismic sensors is no small concern. When North Korea tests a new nuclear weapon, they usually do it underground. For outside monitors, the best source of information about those tests is usually the seismic activity they generate. While the Comprehensive Nuclear-Test-Ban Treaty Organization uses encrypted VPNs to transfer data, making it very difficult to alter seismological data sent from monitoring devices, other independent monitors outside of that organization, such as academics, may not.
Researchers at the Institute of Geodynamics at the National Observatory of Athens found cyber vulnerabilities in several systems used to detect and calculate the location and size of tremors. These include some seismographs; accelerographs, which record the acceleration of the ground with respect to time; and Global Navigation Satellite System, or GNSS, receivers, the team wrote in a study published in the scientific journal Seismological Research Letters. GNSS receivers help measure the “displacement the movement of tectonic plates of just a few millimetres per year, volcano inflation and deflation, and smaller-scale phenomena such as landslides,” according to the UK’s Centre for the Observation and Modelling of Earthquakes, Volcanoes and Tectonics.
In a lab setting, the researchers used “man‐in‐the‐middle” attacks to intercept the data transmitted from a number of common seismographs, accelerographs, and GNSS receivers, to their respective networks.
For the seismographs and accelerographs, they were able to obtain valid usernames. For the GNSS receiver, they were able to get the username and the password.
With password credentials, the researchers found, attackers could manipulate the data. “An example of such an attack is the removal or modification of Global Positioning System time in the data, the change of naming in seismic station code and channels, the change of sampling frequency, and so forth,” they note.
Such manipulation could enable a country that was conducting underground nuclear testing to undermine the ability of the international community to effectively monitor what they were doing, possibly concealing the testing or even embellishing it.
The researchers also found that they could intercept data in the transmission protocol (SeedLink) that the seismograph and accelerograph devices used for network communication. The researchers were able to manipulate SeedLink waveforms, which would interfere with the communication.
And they found that they could simply interrupt the systems’ communications with distributed-denial-of-service attacks.
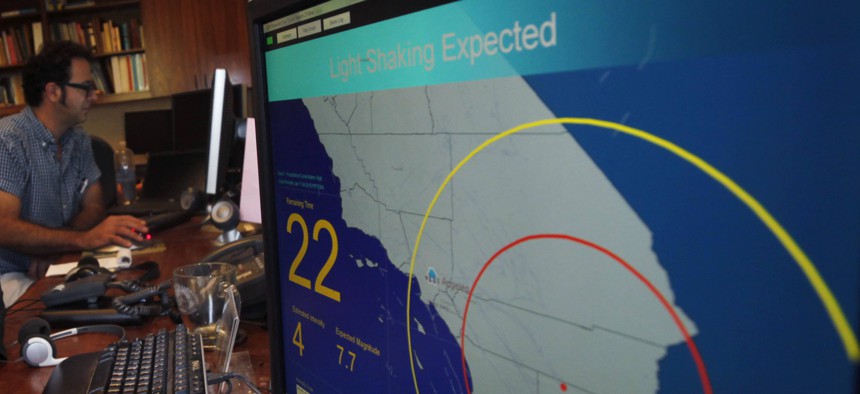
There are also national security ramifications for earthquake detection. A growing number of countries, including the United States, rely on such sensor networks to get early warning of big earthquakes and predict the size of aftershocks. In Japan, for example, the Early Earthquake Warning System sends alerts to phones across the country and even shuts down speeding trains when it detects the small tremors that typically precede much larger ones. The researchers note that an attack on this system “could disrupt operation or even produce false alarms that will trigger all the subsequent automated procedures. These malicious false alarms have considerable consequences such as unnecessary public concern, significant industrial economical losses, and vulnerable national security.”
They don’t reveal the names of the brands of sensors they hacked.
Patrick Tucker is technology editor for Defense One.

NEXT STORY: Maryland Created the Police Officers’ Bill of Rights. Now Lawmakers There Might Repeal It.