sponsor content What's this?
Elements of a Strong Cyber Defense Program for SLTTs

Presented by
Center for Internet Security

It's no secret that developing a robust cyber defense program can be a challenge, especially if you're in the public sector. When you're in charge of protecting sensitive information for a U.S. State, Local, Tribal, or Territorial (SLTT) organization, the pressure can be intense. On top of that, you're faced with a limited budget and staff.
So, where do you start? What exactly should your first step be when developing a cyber defense program?
If you're asking the security experts from the Center for Internet Security (CIS), we'll tell you your first step should be to establish essential cyber hygiene by implementing the CIS Critical Security Controls (CIS Controls).
What Are the CIS Controls and How Can They Help SLTTs?
The CIS Controls are a prioritized set of 18 high-level actions that have been designed to protect your organization and its data from top attack vectors. Each CIS Control includes smaller actions that guide you based on the resources available to you and the risk profile your organization faces. These smaller actions, known as CIS Safeguards, each call for a single action step wherever possible in a way that is clear and requires minimal interpretation. Each Safeguard is focused on measurable actions so you can more easily track your progress in applying effective protection against common attacks. To develop the CIS Controls, we work with a volunteer community of IT and security professionals from around the globe. We share and debate ideas, and we ultimately come to a consensus on recommended actions.
In an effort to further simplify the process of effectively applying the CIS Controls in your organization, CIS created three Implementation Groups (IGs). Every organization, no matter the size or resources, starts with IG1. IG1 is the definition of essential cyber hygiene and represents a minimum standard of information security for all enterprises. Applying all of the Safeguards listed in IG1 will help you thwart general, non-targeted attacks and strengthen your cyber defense program.

Why Essential Cyber Hygiene is Important
The term 'cyber hygiene' was coined at least 20 years ago and is usually attributed to internet pioneer, Vint Cerf. Almost all successful attacks take advantage of conditions that could be described as 'poor hygiene,' including the failure to patch known vulnerabilities, poor configuration management, and inefficient management of administrative privilege.
Cyber hygiene, then, is a set of specific actions – enabled by content, tools, training and services – that track and report the progress of an enterprise-improvement program. In a world where business relationships are complex and linked by technology, this approach provides a specific way to negotiate trust and an expectation of security. Essential cyber hygiene is the concept that applying all of the Safeguards in IG1 will keep your organization safe from most potential cyber-attacks. In fact, it's backed by data from our CIS Community Defense Model. The actions taken from the Safeguards in IG1 defends against 77% of MITRE ATT&CK (sub-)techniques used across the top five attack types. Implement all of the Safeguards in IG2 and IG3, and you can defend yourself against even more potential attacks.
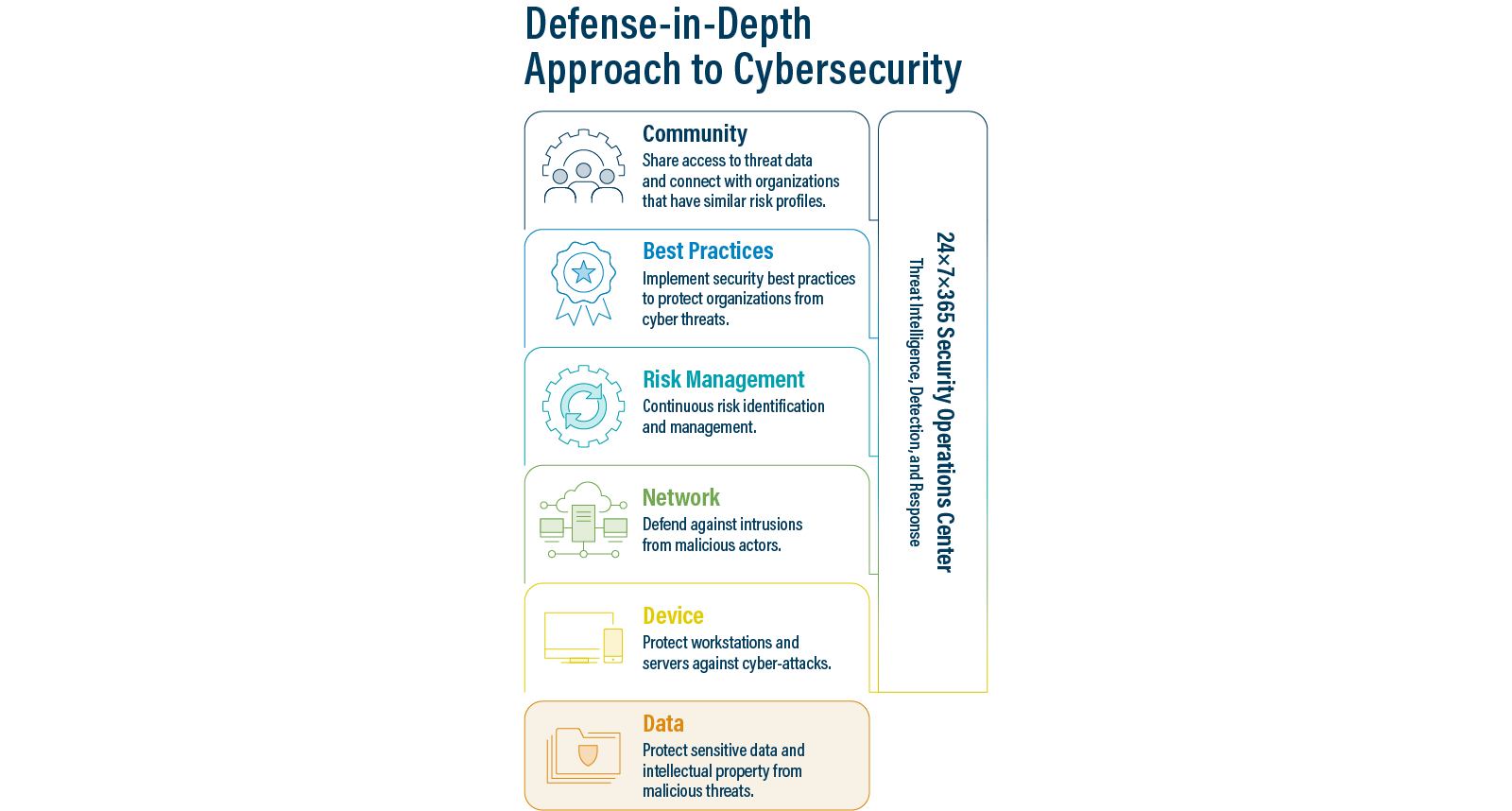
Pairing Essential Cyber Hygiene with Defense-in-Depth
While essential cyber hygiene is very important, it's not the only thing an organization needs to consider. It's simply the foundation. This is where you'll want to include a defense-in-depth approach to cybersecurity. This approach stresses the importance of building layers of controls and mitigations for systems and networks that provide redundancy and reduce the likelihood of a successful cyber-attack or a single point of failure. At CIS, we recommend including these five layers into your defense-in-depth approach to secure data and critical assets:
- Community. Work with the larger community to gain access to threat alert data and connect with organizations that have similar risk profiles.
- Best Practices. Implement security best practices to protect organizations from cyber threats.
- Risk Management. Identify and prepare for a range of cybersecurity risks.
- Network. Defend against intrusions from malicious actors.
- Device. Protect workstations and servers against cyber-attacks.
- Data. Identify, classify, securely handle, retain, and dispose of data.
Layering Tactics for a Stronger Cyber Defense Program
A critical element of your defense-in-depth strategy is effective device-level protection. Through CIS, public entities have access to CIS Endpoint Security Services. This fully-managed service offers active defense against both known (signature-based) and unknown (behavioral-based) malicious activity. This additional layer of security is deployed directly on devices like workstations and servers and will identify, detect, respond to, and remediate security incidents and alerts.
With remote work becoming more prevalent due to the COVID-19 pandemic, CIS Endpoint Security Services allows your entity to protect remote devices just as easily as it does on-network devices. Those devices are monitored and managed 24x7x365 by the CIS Security Operations Center (SOC), where expert analysts serve as full-time cybersecurity defense partners in analyzing malicious activity and escalating actionable threats. When an entity experiences an incident, they also have the full support of our Cyber Incident Response Team (CIRT) to investigate the incident and help identify its root cause. SLTTs can use this as a learning opportunity to help prevent future system compromises. The image below shows the full capabilities of CIS Endpoint Security Services.

Endpoint Security and Controls Implementation: Stronger Together
Combining essential cyber hygiene and tools or services based on layers from the defense-in-depth strategy significantly increases the time and complexity required for bad actors to successfully compromise a network. This increases the chance that an active attack can be identified and mitigated before it's successful.
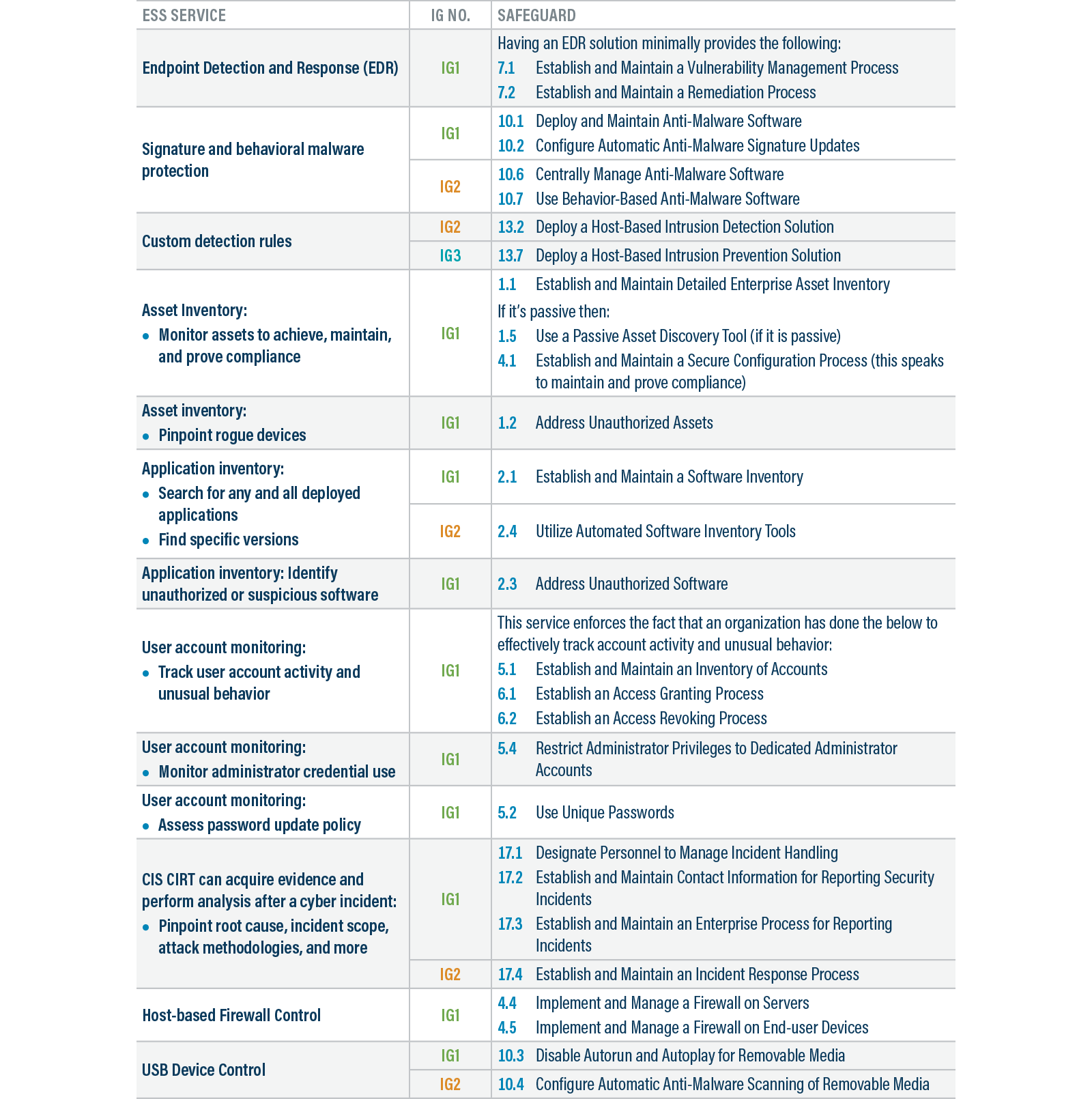
For a deeper understanding of how CIS Endpoint Security Services complements the CIS Controls, review the chart below.
NEXT STORY: Is 2022 the Year Cybersecurity Goes Mainstream?



