Election Security Threats Loom As Midterms Near, State Officials Say
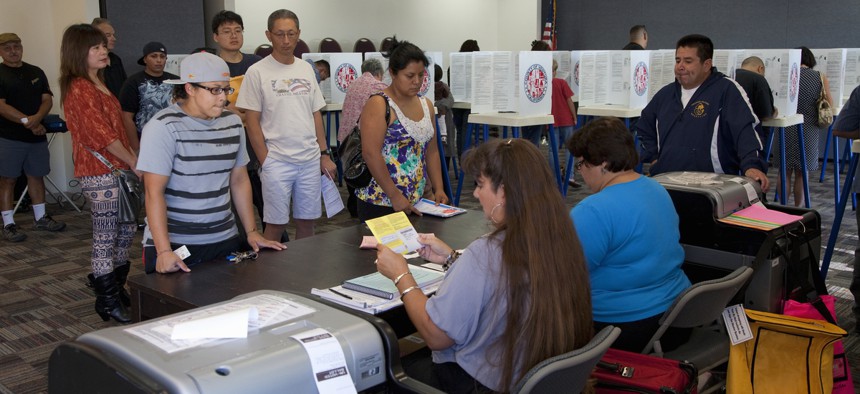
Voters at a polling station in the 2012 Presidential Election on Nov. 06, 2012 in Ventura County, California. Shutterstock
But some note progress. “I think we’re in a much better position than two years ago,” says Minn. Secretary of State Steve Simon.
WASHINGTON — The federal government is doing a better job providing information and money to states to help combat election security threats, but there’s still room for improvement, secretaries of state said here on Wednesday.
Secretaries of state from Minnesota, Missouri, and Vermont testified before the Senate Rules and Administration Committee about election security. The topic has gained attention at the state and federal levels in the wake of the 2016 election cycle when, according to U.S. intelligence officials, Russian-linked hackers probed election systems in at least 21 states.
“During the 2016 election cycle, state and local election officials were tested like they haven’t been before by cyberattacks and we anticipate that these attempts will continue,” said Sen. Roy Blunt, the Missouri Republican who chairs the Rules and Administration Committee.
With Election Day in the 2018 midterms 139 days away, and primaries underway, voting security remains a hot issue, one that has at times led to tensions between states and the feds.
“Election security in general, and cybersecurity in particular, poses the number one threat to the integrity of our elections,” said Minnesota Secretary of State Steve Simon, a Democrat.
State election officials and others emphasize that no evidence has emerged that hackers improperly changed any votes, or voter registration information in 2016.
“It was not our votes, or our election systems that were hacked, it was the people’s perception of our elections,” Missouri Secretary of State Jay Ashcroft, a Republican, told the Senate panel.
Nationwide at least 40 secretaries of state serve as their state’s chief election official. Since 2016, some have chafed over what they’ve described as sluggish and incomplete election security information-sharing by the Department of Homeland Security with states.
Route Fifty asked Simon after the hearing if those concerns had been resolved. “Resolved is a very final word,” he replied. “Resolved ultimately? No.” But he added: “I give DHS credit for going a long way toward ensuring that in 2018 we have better lines of communication.”
He said a group known as the Elections Government Sector Coordinating Council, in particular, has been helpful getting state, local and federal officials “on the same page” when it comes to communications protocols for election security.
“I think we’re in a much better position than two years ago,” Simon added.
Speeding up the delivery of information about security threats to states is one area where Simon would like to see improvement. He said Minnesota did not confirm until 10 months after the 2016 general election that it was one of the 21 states that hackers targeted.
Vermont Secretary of State Jim Condos, a Democrat, agreed that information sharing between the feds and states is improving. “If one state, or one locale, is hacked, or breached, or attacked, we all have to be considered under attack,” he told Route Fifty after the hearing.
Condos and Simon both said they’d obtained security clearances, something identified in recent months as a key step for state election leaders to gain greater access to security intelligence.
Matt Masterson, a senior cybersecurity advisor with the Department of Homeland Security, also testified on Wednesday. "We hear the criticism," he said when asked after the hearing about information-sharing with states. But he said that in any "sector that's maturing" there tend to be questions about how to best share information.
"There's actually been a lot of information shared," he added.
Masterson also noted that this material does not necessarily have to be about specific threats, and could also be about best practices or guidelines for protecting computer systems.
Congress earlier this year allotted $380 million for election security grants to states under the Help America Vote Act. As of Tuesday, states had requested about $260 million, or 68 percent, of the so-called “HAVA” funds, according to the U.S. Election Assistance Commission.
Condos applauded the commission for moving swiftly to provide the money and said his state had requested and received $3 million, which it plans to put toward efforts like implementing “two-factor authentication,” for local clerks and other staff who use election management systems, and for conducting “penetration testing” on computer systems.
Simon expressed appreciation for the money, but added that Congress should consider how to provide states with election security funding on an ongoing basis. He also pointed out that the half-life of election security measures can be short, given how quickly threats evolve.
“This is a race without a finish line,” he said.
During the hearing, the committee’s top Democrat, Sen. Amy Klobuchar, of Minnesota, touted bipartisan election security legislation that she and other senators have been pushing.
One part of the bill calls for an advisory panel to develop guidelines for election cybersecurity, including audits, which involve checking voting results to ensure they’re accurate. It also includes provisions for grants to reimburse states for audit expenses.
“We want an audit,” Klobuchar told reporters after the hearing.
All three of the secretaries of state on hand Wednesday said their states require a paper trail that allows for audits. Blunt asked them if they thought there should be a national requirement for states to have paper voting records for audits to access federal assistance.
Ashcroft said he didn’t think so. Condos said he did think so. And Simon said there’s a federal interest in making sure that there’s some type of audit process.
“I believe states are moving to do that without federal legislation,” Ashcroft said.
Ashcroft displayed somewhat of a rift with the other two secretaries of state in how he characterized the challenges confronting the nation’s election system. During the hearing, he highlighted voter fraud as a risk, and cited a 2010 Missouri state House race that was decided by one vote and where authorities later determined two people cast illegal ballots.
“Voter fraud is an exponentially greater threat than hacking of our election equipment,” he told lawmakers.
He also said that when people get the mistaken impression that votes have been changed by foreign actors or hacking, it has the potential to depress voter turnout.
“We are encouraging people, I assume unintentionally, to stay home,” he said.
Ashcroft is pushing for what he calls a “comprehensive approach” to election security that involves stopping fraud, other illegal behavior, and “ineptitude” from affecting voting outcomes.
Election security experts and others have stressed repeatedly that there is no evidence of widespread voter fraud in the U.S.
President Trump in January disbanded a commission the White House had formed to explore the issue. It, too, failed to produce concrete evidence of widespread fraud.
“From my perspective, the true voter fraud in this country is eligible Americans that are denied the opportunity to cast a ballot,” Condos said. In Vermont, he added, 68 percent of eligible voters turned out in 2016. “We have trouble enough getting people to vote once, never mind twice.”
Bill Lucia is a Senior Reporter for Government Executive's Route Fifty and is based in Washington, D.C.
NEXT STORY: Feds Block States From Developing on Land That Could Belong to Frogs






